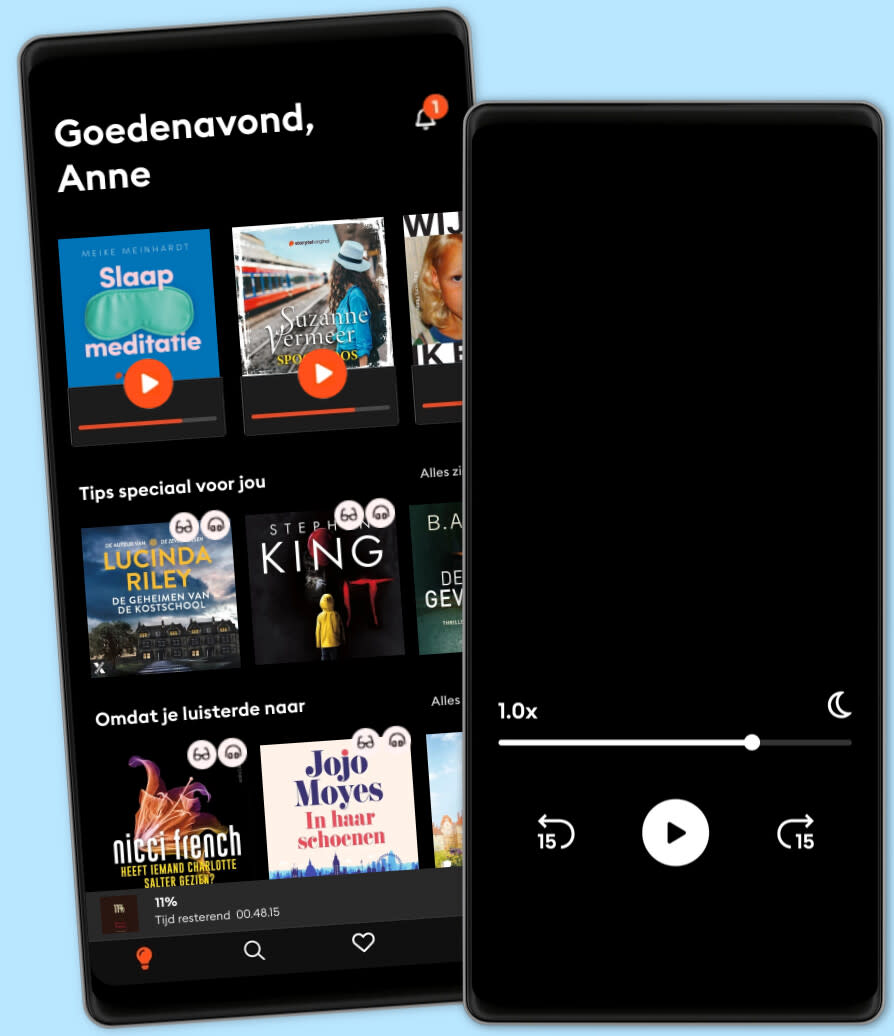
Luisterboeken voor iedereen
Meer dan 1 miljoen luisterboeken en ebooks in één app. Ontdek Storytel nu.
- Switch makkelijk tussen luisteren en lezen
- Elke week honderden nieuwe verhalen
- Voor ieder een passend abonnement
- Opzeggen wanneer je maar wilt
Cyberdeterrence and Cyberwar
- Door
- Met
- Uitgever
- 10 beoordelingen
3.6
- Lengte
- 6uur 8min
- Taal
- Engels
- Format
- Categorie
Geschiedenis
The protection of cyberspace, the information medium, has become a vital national interest because of its importance both to the economy and to military power. An attacker may tamper with networks to steal information for money or to disrupt operations. Future wars are likely to be carried out, in part or perhaps entirely, in cyberspace. It might seem that maneuvering in cyberspace is like maneuvering in other media, but nothing would be more misleading. Cyberspace has its own laws. It is easy to hide identities and difficult to predict or even understand battle damage, and attacks deplete themselves quickly. Cyberwar is nothing so much as the manipulation of ambiguity.
Martin Libicki explores these topics in detail and uses the results to address such issues as the pros and cons of counterattack, the value of deterrence and vigilance, and other defensive actions the United States and the US Air Force can take in the face of deliberate cyberattack.
© 2011 Blackstone Publishing (Luisterboek): 9781481554336
Publicatiedatum
Luisterboek: 8 februari 2011
Anderen genoten ook van...
- America’s Secret War: Inside the Hidden Worldwide Struggle between America and its Enemies George Friedman
- The Black Door: Spies, Secret Intelligence and British Prime Ministers Richard Aldrich
- Cybersecurity and Cyberwar: What Everyone Needs to Know Allan Friedman
- The New Rules of War: Victory in the Age of Durable Disorder Sean McFate
- Russians Among Us: Sleeper Cells, Ghost Stories, and the Hunt for Putin’s Spies Gordon Corera
- Permanent Record: A Memoir of a Reluctant Whistleblower Edward Snowden
- The CIA as Organized Crime: How Illegal Operations Corrupt America and the World Douglas Valentine
- The Shadow War: Inside Russia's and China's Secret Operations to Defeat America Jim Sciutto
- Ghost: Confessions of a Counterterrorism Agent Fred Burton
- Body of Secrets: Anatomy of the Ultra-Secret National Security Agency James Bamford
- Dodelijk spoor (1) Barbara De Smedt
4.3
- De leraar: Deze les zal ze nooit meer vergeten... Freida McFadden
4.3
- Bechamel Mucho Dimitri Verhulst
4
- It ends with us: Nooit meer is de Nederlandse uitgave van It Ends With Us Colleen Hoover
4.4
- Het Pumpkin Spice Café: Het seizoen om verliefd te worden Laurie Gilmore
3.6
- Operatie T.O.I.L.E.T. Timon Verbeeck
4.7
- Slaapmeditatie: 30 minuten meditatie voor ontspanning en slaap Meike Meinhardt
4.2
- Het moois dat we delen Ish Ait Hamou
4.5
- Omringd door idioten: Beter communiceren met collega's, vrienden en familie Thomas Erikson
4.1
- It starts with us: Vanaf nu is de Nederlandse uitgave van het vervolg op It Ends With Us Colleen Hoover
4.3
- De hulp: Vanachter gesloten deuren ziet zij alles... Freida McFadden
4.4
- Over je toeren Manon Borgen
3.7
- Dodelijk spoor (2) Barbara De Smedt
4.2
- Hoe we onszelf graag kunnen zien: Over grenzen stellen, perfectionisme, people pleasing, zelfsabotage en ware veerkracht Onbespreekbaar
4.5
- Slaapmeditatie: 15 minuten Meike Meinhardt
4.6
Maak je keuze:
Voor ieder een passend abonnement
Kies het aantal uur en accounts dat bij jou past
Download verhalen voor offline toegang
Kids Mode - een veilige omgeving voor kinderen
Unlimited
Voor wie onbeperkt wil luisteren en lezen.
1 account
Onbeperkte toegang
Meer dan 1 miljoen luisterboeken en ebooks
Altijd opzegbaar
Premium
Voor wie zo nu en dan wil luisteren en lezen.
1 account
30 uur/maand
Meer dan 1 miljoen luisterboeken en ebooks
Altijd opzegbaar
Flex
Voor wie Storytel wil proberen.
1 account
10 uur/30 dagen
Spaar ongebruikte uren op tot 50 uur
Meer dan 1 miljoen luisterboeken en ebooks
Altijd opzegbaar
Family
Voor wie verhalen met familie en vrienden wil delen.
2-3 accounts
Onbeperkte toegang
Meer dan 1 miljoen luisterboeken en ebooks
Altijd opzegbaar
2 accounts
€18.99 /30 dagenNederlands
België