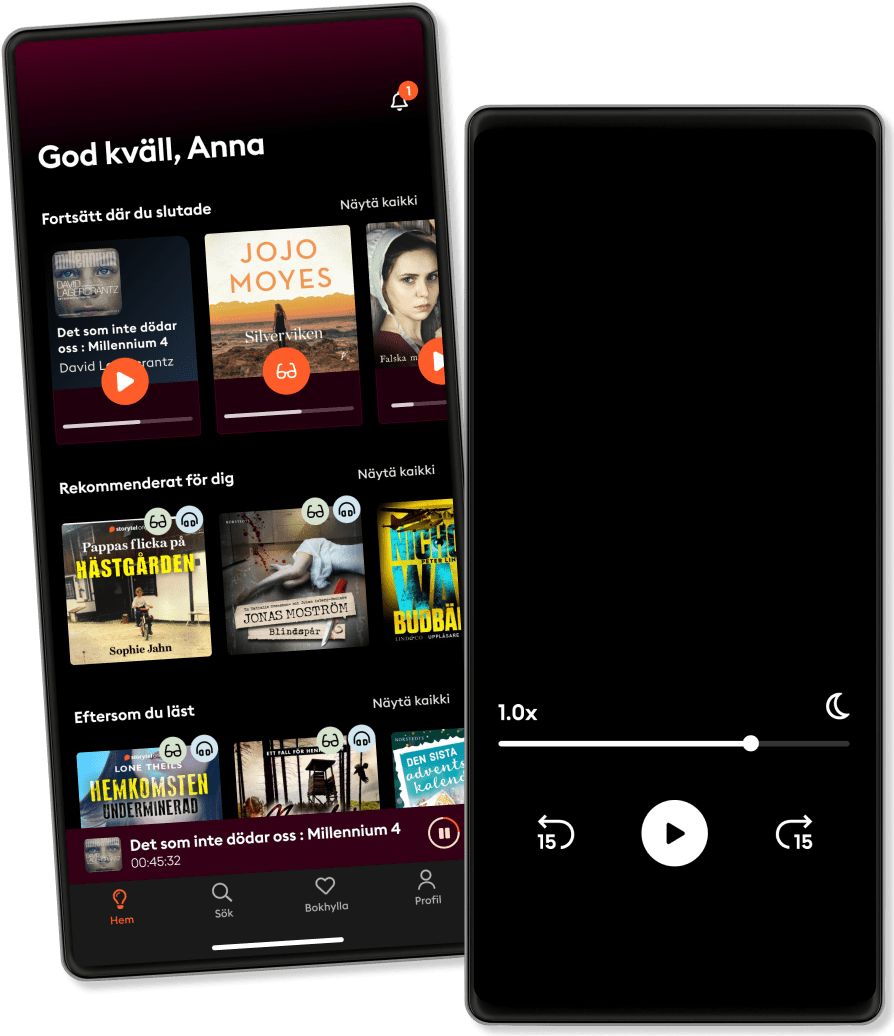
الاستماع والقراءة
خطوة إلى عالم لا حدود له من القصص
- اقرأ واستمع إلى ما تريده
- أكثر من مليون عنوان
- العناوين الحصرية + أصول القصة
- 7 الشهر يورو في EGP89 يوم تجربة مجانية، ثم
- من السهل الإلغاء في أي وقت
Network Security Fundamentals: Security Architecture & Design Principles
- بواسطة
- مع:
- الناشر
- 1 التقييمات
5
- المدة
- 3H 5دقيقة
- اللغة
- اللغة الإنجليزية
- Format
- الفئة
كتب واقعية
If you want to become a Cybersecurity Professional, this book is for you!
If you are studying for CompTIA Security+ or CISSP, this book will help you pass your exam. Passing security exams isn’t easy. In fact, due to the raising security beaches around the World, both above mentioned exams are becoming more and more difficult to pass. Whether you want to become an Infrastructure Engineer, IT Security Analyst or any other Cybersecurity Professional, this book (as well as the other books in this series) will certainly help you get there!
GET THIS BOOK NOW AND START LEARNING TODAY!
In this book you will discover: Baseline Configuration, Diagrams & IP Management Data Sovereignty & Data Loss Prevention Data Masking, Tokenization & Digital Rights Management Geographical Considerations & Cloud Access Security Broker Secure Protocols, SSL Inspection & Hashing API Gateways & Recovery Sites Honeypots, Fake Telemetry & DNS Sinkhole Cloud Storage and Cloud Computing IaaS, PaaS & SaaS Managed Service Providers, Fog Computing & Edge Computing VDI, Virtualization & Containers Microservices and APIs Infrastructure as Code (IAC) & Software Defined Networking (SDN) Service Integrations and Resource Policies Environments, Provisioning & Deprovisioning Integrity Measurement & Code Analysis Security Automation, Monitoring & Validation Software Diversity, Elasticity & Scalability Directory Services, Federation & Attestation Time-Based Passwords, Authentication & Tokens Proximity Cards, Biometric & Facial Recognition Vein and Gait Analysis & Efficacy Rates
GET THIS BOOK NOW AND START LEARNING TODAY!
© 2022 PublishDrive (دفتر الصوت ): 9781839381690
تاريخ الإصدار
دفتر الصوت : ١٧ ديسمبر ٢٠٢٢
الوسوم
واستمتع آخرون أيضًا...
- Computer Networking: Network+ Certification Study Guide for N10-008 Exam 4 Books in 1: Enterprise Network Infrastructure, Network Security & Network Troubleshooting Fundamentals Richie Miller
- Cybersecurity For Dummies Joseph Steinberg
- CISSP Exam Study Guide For Information Security Professionals: Beginners Guide To Cybersecurity Threats, Ethical Hacking And Defense Techniques 3 Books In 1 John Knowles
- Cloud Security For Dummies Ted Coombs
- Cybersecurity Fundamentals: How to Establish Effective Security Management Functions John Knowles
- Cyber Security: How to Protect Your Digital Life, Avoid Identity Theft, Prevent Extortion, and Secure Your Social Privacy in 2020 and beyond Matt Reyes
- Microsoft Azure Security And Privacy Concepts: Cloud Deployment Tools And Techniques, Security & Compliance Richie Miller
- Cybersecurity Design Principles: 2 Books In 1: Building Secure Resilient Architecture Richie Miller
- CISSP Exam Study Guide For Cybersecurity Professionals: 2 Books In 1: Beginners Guide To Nist Cybersecurity Framework & Risk Management Governance Strategies HUGO HOFFMAN
- Hacking the Hacker: Learn From the Experts Who Take Down Hackers Roger A. Grimes
- أسطورة أحمد خالد توفيق - E01 خلف جابر
4.4
- ملخص كتاب الذكاء العاطفي ترافيس برادبيري
3.3
- ملخص كتاب عقل هادئ: كيف توقف التوتر وتحدّ من نوبات القلق وتقضي على التفكير السلبي ستيف سكوت
4.3
- أرض زيكولا عمرو عبدالحميد
4.1
- ملخص كتاب قوانين الكاريزما كيرت مورتنسن
3.8
- ملخص كتاب فن اللامبالاة مارك مانسون
3.7
- ملخص كتاب كيف تتحدث مع أي شخص 92 خدعة صغيرة: اثنتان وتسعون خدعة صغيرة، لنجاح كبير في العلاقات ليل لاوندز
3.6
- أوراق شمعون المصري الموسم الأول أسامة عبد الرءوف الشاذلي
4.7
- ملخص كتاب دماغك تحت تأثير الإباحية غاري ويلسون
4.2
- معاطي Nani Abu Rawash
4.1
- أغنية الجليد والنار: لعبة العروش جورج ر. ر. مارتن
4.6
- المطارد حسن الجندي
4.5
- 30 يوما مع الله فيصل أحمد بخاري
4.6
- العادات الذرية جيمس كلير
4.5
- فن اللامبالاة: لعيش حياة تخالف المألوف مارك مانسون
4.3
ما مميزات اشتراك Storytel؟
أكثر من 200000 عنوان
وضع الأطفال (بيئة آمنة للأطفال)
تنزيل الكتب للوصول إليها دون الاتصال بالإنترنت
الإلغاء في أي وقت
شهري
قصص لكل المناسبات.
حساب واحد
حساب بلا حدود
1 حساب
استماع بلا حدود
إلغاء في أي وقت
سنويا
قصص لكل المناسبات.
حساب واحد
حساب بلا حدود
1 حساب
استماع بلا حدود
إلغاء في أي وقت
6 أشهر
قصص لكل المناسبات.
حساب واحد
حساب بلا حدود
1 حساب
استماع بلا حدود
إلغاء في أي وقت
عربي
مصر