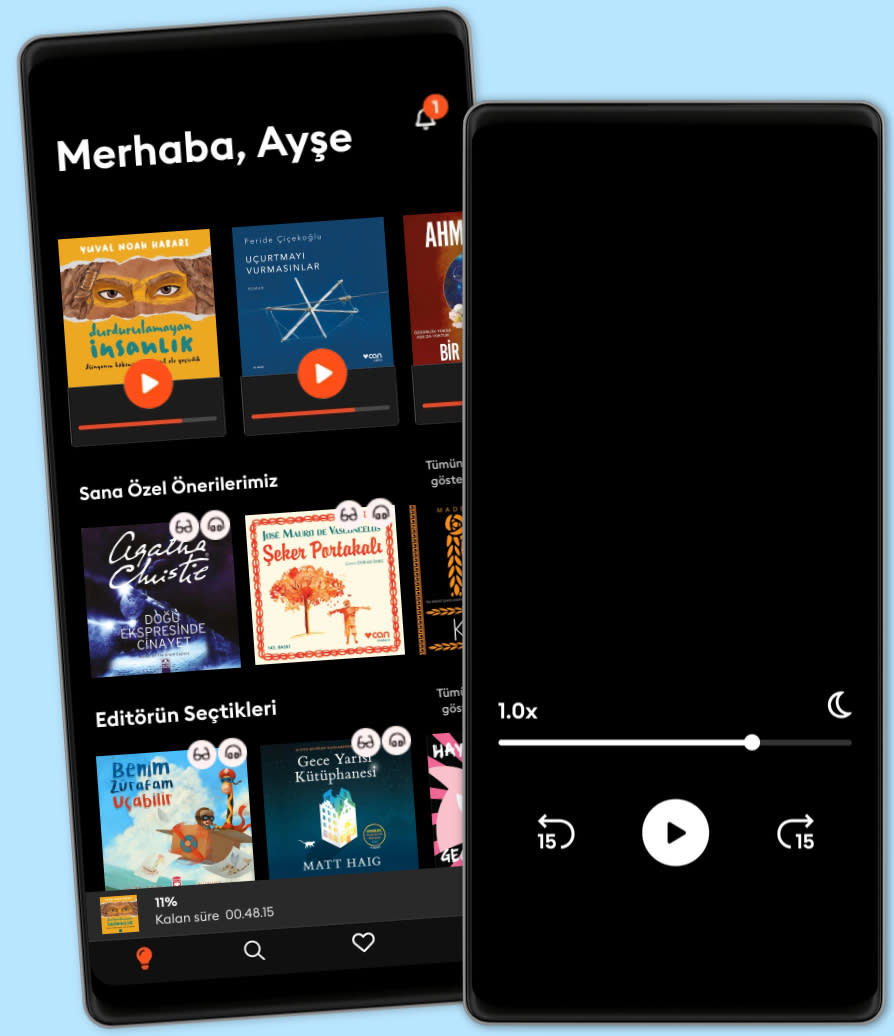
Dinle ya da oku
Sesli kitapların büyülü dünyasına adım at.
- İlk 2 ay ₺99,99/ay
- Binlerce sesli kitap ve e-kitap.
- Dilediğin kadar dinle ya da oku.
- Çevrimdışı modu.
- İstediğin zaman iptal et.
Cybersecurity - Attack and Defense Strategies: Infrastructure security with Red Team and Blue Team tactics
- Yazan
- Yayınevi
- Dil
- İngilizce
- Format
- Kategori
Kurgu Dışı
The book will start talking about the security posture before moving to Red Team tactics, where you will learn the basic syntax for the Windows and Linux tools that are commonly used to perform the necessary operations. You will also gain hands-on experience of using new Red Team techniques with powerful tools such as python and PowerShell, which will enable you to discover vulnerabilities in your system and how to exploit them. Moving on, you will learn how a system is usually compromised by adversaries, and how they hack user's identity, and the various tools used by the Red Team to find vulnerabilities in a system.
In the next section, you will learn about the defense strategies followed by the Blue Team to enhance the overall security of a system. You will also learn about an in-depth strategy to ensure that there are security controls in each network layer, and how you can carry out the recovery process of a compromised system. Finally, you will learn how to create a vulnerability management strategy and the different techniques for manual log analysis.
© 2018 Packt Publishing (E-Kitap): 9781788473859
Yayın tarihi
E-Kitap: 30 Ocak 2018
Etiketler
Bunları da beğenebilirsin...
- Cybersecurity and Cyberwar: What Everyone Needs to Know Allan Friedman
- FAIK: A Practical Guide to Living in a World of Deepfakes, Disinformation, and AI-Generated Deceptions Perry Carpenter
- A Leader’s Guide to Cybersecurity: Why Boards Need to Lead-And How to Do It Jack J. Domet
- The Internet Is Not What You Think It Is: A History, a Philosophy, a Warning Justin Smith-Ruiu
- Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World Bruce Schneier
- The NSA Report: Liberty and Security in a Changing World Richard A. Clarke
- Navigating Cybersecurity and Ethical Hacking: The Art of Ethical Hacking: Exploring Cybersecurity from Within Lily Grayson
- See Yourself in Cyber: Security Careers Beyond Hacking Ed Adams
- Cybersecurity: The Hacker Proof Guide to Cybersecurity, Internet Safety, Cybercrime, & Preventing Attacks Trust Genics
- Distrust: Big Data, Data-Torturing, and the Assault on Science Gary Smith
- Rezonans Kanunu Pierre Franckh
4.3
- Dünyanın En Önemli Öğrencisi Şermin Yaşar
4.7
- İnce Memed 1 Yaşar Kemal
4.9
- Yırtıcı Kuşlar Zamanı Ahmet Ümit
4.7
- Beni Gözünüzde Büyütmeyin! Gülse Birsel
4.6
- Kral Kaybederse Gülseren Budayıcıoğlu
4.7
- Palto Nikolay Gogol
4.6
- 4 Gün 3 Gece Ayşe Kulin
4.1
- Gece Yarısı Kütüphanesi Matt Haig
4.6
- Bir Delinin Hatıra Defteri Nikolay Gogol
4.3
- İnce Memed 2 Yaşar Kemal
4.8
- İnce Memed 3 Yaşar Kemal
4.9
- Kürk Mantolu Madonna Sabahattin Ali
4.5
- Harry Potter ve Felsefe Taşı J.K. Rowling
4.3
- Handan Ayşe Kulin
4.2
Storytel dünyasını keşfet:
Kids mode
Çevrimdışı modu
İstediğin zaman iptal et
Her yerde erişim
Sınırsız
Sınırsızca dinlemek ve okumak isteyenler için.
1 hesap
Sınırsız erişim
İstediğin zaman iptal et
Sınırsız Yıllık
Sınırsızca dinlemek ve okumak isteyenler için.
1 hesap
Sınırsız erişim
İstediğin zaman iptal et
Aile (2 hesap)
Hikayeleri sevdikleri ile paylaşmak isteyenler için.
2 hesap
Sınırsız erişim
İstediğin zaman iptal et
Aile (3 hesap)
Hikayeleri sevdikleri ile paylaşmak isteyenler için.
3 hesap
Sınırsız erişim
İstediğin zaman iptal et
Türkçe
Türkiye