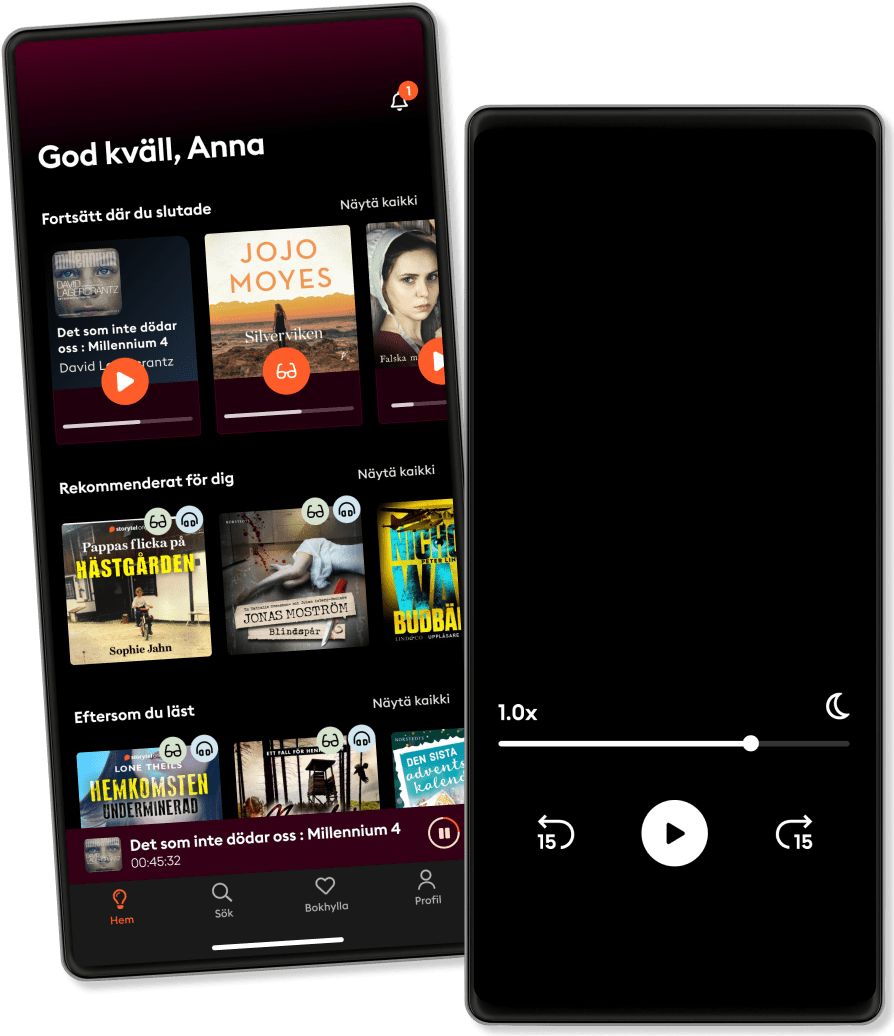
Listen and read
Step into an infinite world of stories
- Read and listen as much as you want
- Over 950 000 titles
- Exclusive titles + Storytel Originals
- Easy to cancel anytime
Some Examples Related to Ethical Computer Networking Hacking
- By
- Publisher
- Language
- English
- Format
- Category
Non-Fiction
The objective of this work is to provide some quick tutorials in computer networking hacking.
The work includes the following tutorials:
- Tutorial 1: Setting Up Penetrating Tutorial in Linux
- Tutorial 2: Setting Up Penetrating Tutorial in Windows
- Tutorial 3: OS Command Injection
- Tutorial 4: Basic SQL Injection Commands
- Tutorial 5: Manual SQL injection using order by and union select technique
- Tutorial 6: Damping SQL Tables and Columns Using the SQL Injection
- Tutorial 7: Uploading Shell in the Site having LFI
- Tutorial 8: Advanced Way for Uploading Shell
- Tutorial 9: Uploading shell Using Sqli Command
- Tutorial 10: Uploading Shell Using SQLmap
- Tutorial 11: Post Based SQL Injection
- Tutorial 12: Cracking the Hashes Using
- Tutorial 13: Hacking windows 7 and 8 through Metasploite
- Tutorial 14: Tutorial on Cross Site Scripting
- Tutorial 15: Hacking Android Mobile Using Metasploit
- Tutorial 16: Man of the middle attack
- Tutorial 17: Using SQLmap for SQL injection
- Tutorial 18: Hide Your Ip
- Tutorial 19: Uploading Shell and Payloads Using SQLmap
- Tutorial 20: Using Sql Shell in SQLmap
- Tutorial 21: Blind SQL Injection
- Tutorial 22: Jack Hridoy SQL Injection Solution
- Tutorial 23: Using Hydra to Get the Password - Tutorial 24: Finding the phpmyadmin page using websploit
- Tutorial 25: How to root the server using back connect
- Tutorial 25: How to root the server using back connect
- Tutorial 26: HTML Injection
- Tutorial 27: Tutuorial in manual SQl Injection
- Tutorial 28: Venom psh-cmd-exe payload
- Tutorial 29: Cross site Request Forgery (CSRF)
- Tutorial 30: Disable Victim Computer
- Tutorial 31: Exploit any firefox by xpi_bootstrapped addon
- Tutorial 32: Hack android mobile with metasploit
- Tutorial 33: PHP Code Injection to Meterpreter Session
- Tutorial 34: Basic google operators
- Tutorial 35: Hacking Credit Cards with google
- Tutorial 36: Finding Vulnerable Websites in Google
- Tutorial 37: Using the httrack to download website
- Tutorial 38: Getting the credit cards using sql injection and the SQLi dumper
- Tutorial 39: Using burp suite to brute force password
© 2020 BookRix (Ebook): 9783748767565
Release date
Ebook: 7 December 2020
Others also enjoyed ...
- Cyber Smart: Five Habits to Protect Your Family, Money, and Identity from Cyber Criminals Bart R. McDonough
- Social Engineering: The Science of Human Hacking 2nd Edition Christopher Hadnagy
- Hacking the Hacker: Learn From the Experts Who Take Down Hackers Roger A. Grimes
- Cybersecurity For Dummies Joseph Steinberg
- Hacker, Hoaxer, Whistleblower, Spy: The Many Faces of Anonymous Gabriella Coleman
- Cybersecurity and Cyberwar: What Everyone Needs to Know Allan Friedman
- Python: - The Bible- 3 Manuscripts in 1 book: Python Programming for Beginners - Python Programming for Intermediates - Python Programming for Advanced Maurice J. Thompson
- Electronic Health Records for Dummies Anita Samarth
- Greatest Hackers in the History Introbooks Team
- Exploding Data: Reclaiming Our Cyber Security in the Digital Age Michael Chertoff
- Harry Potter and the Philosopher's Stone J.K. Rowling
4.7
- Lights Out: An Into Darkness Novel Navessa Allen
4.5
- Fourth Wing (1 of 2) [Dramatized Adaptation]: The Empyrean 1 Rebecca Yarros
4.7
- A Court of Thorns and Roses (1 of 2) [Dramatized Adaptation]: A Court of Thorns and Roses 1 Sarah J. Maas
4.3
- Fourth Wing (2 of 2) [Dramatized Adaptation]: The Empyrean 1 Rebecca Yarros
4.8
- My Weird School Special: Hip, Hip, Hooray! Every Day Is a Holiday! Dan Gutman
4.8
- Fourth Wing Rebecca Yarros
4.6
- From Blood and Ash (2 of 2) [Dramatized Adaptation]: Blood and Ash 1 Jennifer L. Armentrout
4.4
- HOW TO WIN FRIENDS & INFLUENCE PEOPLE Dale Carnegie
4.3
- Twisted Love Ana Huang
3.7
- Don't Let The Pigeon Drive The Bus Mo Willems
4.4
- Summary of Atomic Habits by James Clear Best Self Audio
4.3
- From Blood and Ash (1 of 2) [Dramatized Adaptation]: Blood and Ash 1 Jennifer L. Armentrout
4.3
- Die With Zero: Getting All You Can from Your Money and Your Life Bill Perkins
4.3
- Broken Bonds J Bree
4.2
Features:
Over 950 000 titles
Kids Mode (child safe environment)
Download books for offline access
Cancel anytime
Unlimited
For those who want to listen and read without limits.
1 account
Unlimited Access
Unlimited listening
Cancel anytime
Unlimited Bi-yearly
For those who want to listen and read without limits.
1 account
Unlimited Access
Unlimited listening
Cancel anytime
Unlimited Yearly
For those who want to listen and read without limits.
1 account
Unlimited Access
Unlimited listening
Cancel anytime
Family
For those who want to share stories with family and friends.
2-3 accounts
Unlimited Access
Unlimited listening
Cancel anytime
2 accounts
S$14.90 /monthEnglish
Singapore