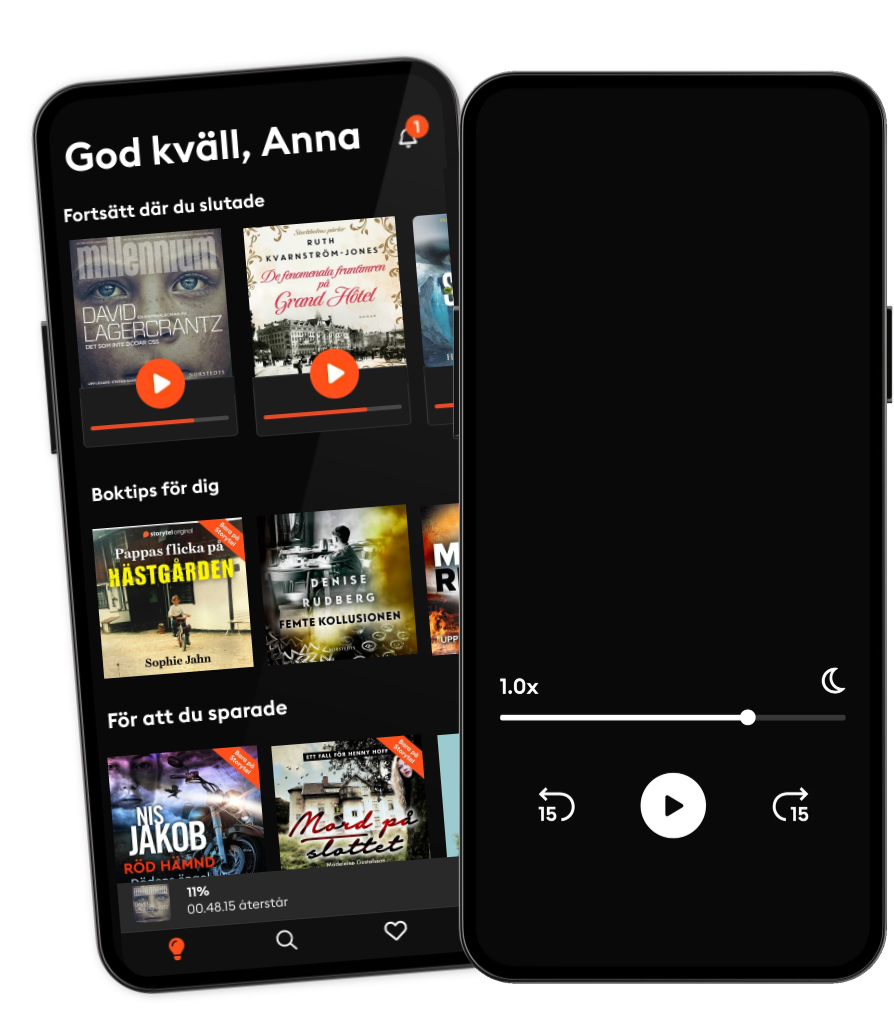
Lyssna när som helst, var som helst
Kliv in i en oändlig värld av stories
- 1 miljon stories
- Hundratals nya stories varje vecka
- Få tillgång till exklusivt innehåll
- Avsluta när du vill
Phishing Training A Complete Guide - 2024 Edition
- Av
- Förlag
- Språk
- Engelska
- Format
- Kategori
Ekonomi & Business
Are network, endpoint, cloud, and discovery all offered from the potential vendor?
Are the information security strategy and IT services bringing value to the business?
Do you engage your employees in phishing training exercises on a regular basis?
Does the security tool use any kind of protection for the web browsers and email clients?
Has there been unauthorised access to, disclosure or loss of personal information?
Is the personal information still being shared, disclosed, or lost without authorisation?
What are the protection levels for confidentiality, integrity, and availability?
What is the trusts strategy for stakeholder engagement, openness and disclosure?
What parties have gained or may gain unauthorised access to the personal information?
Why is cyber exposures by small businesses middle market large businesses important?
This Phishing Training Guide breaks away from traditional books. If you're seeking a standard textbook, this may not be the right fit for you. This guide along with its accompanying digital resources is for you who understands the importance of asking profound questions. This equips you with the questions necessary to uncover the Phishing Training challenges you're confronting and devise superior solutions to address these issues.
Defining, designing, creating, and implementing a process to solve a challenge or achieve an objective is the most valuable role… Get Stuff Done in EVERY group, company, organization and department.
Unless you are dealing with a one-time, single-use project, there should be a process. That process needs to be designed by someone with a broad enough perspective to ask the right questions. Someone able to ask the right questions and step back and say, 'What are we really trying to accomplish here? And is there a different way to look at it?'
This Self-Assessment empowers people to do just that - whether their title is entrepreneur, manager, consultant, (Vice-)President, CxO etc... - they are the people who shape the future. They are the person who asks the right questions to make Phishing Training investments work better.
This Phishing Training All-Inclusive Self-Assessment enables You to be that person.
INCLUDES all the tools you need to an in-depth Phishing Training Self-Assessment. Featuring new and updated case-based questions, organized into seven core levels of Phishing Training maturity, this Self-Assessment will help you identify areas in which Phishing Training improvements can be made.
In using the questions you will be better able to:
Assess Phishing Training projects, initiatives, organizations, businesses and processes using established diagnostic standards and practices.
Implement evidence-based best practice strategies aligned with overall goals.
Integrate recent advances in Phishing Training and process design strategies into practice according to best practice guidelines.
Using the Self-Assessment tool gives you the Phishing Training Scorecard, enabling you to develop a clear picture of which Phishing Training areas need attention.
Your purchase includes access to the Phishing Training self-assessment digital components which gives you your dynamically prioritized project-ready tool. This tool enables you to define, show and lead your organization exactly with what's important.
© 2023 5STARCooks (E-bok): 9781038811288
Utgivningsdatum
E-bok: 3 november 2023
Andra gillade också ...
- Security Policies A Complete Guide - 2024 Edition Gerardus Blokdyk
- Risk Assessments A Complete Guide - 2021 Edition Gerardus Blokdyk
- Ethical Hacking Introbooks Team
- Phishing Attacks A Complete Guide - 2024 Edition Gerardus Blokdyk
- Infosec Strategies and Best Practices: Gain proficiency in information security using expert-level strategies and best practices Joseph MacMillan
- Cybercrime Investigators Handbook Graeme Edwards
- Internet Scams: Money Adders Like PayPal and Bitcoin Scams Exposed David Money
- Microsoft Information Protection Administrator SC-400 Certification Guide: Advance your Microsoft Security & Compliance services knowledge and pass the SC-400 exam with confidence Viktor Hedberg
- Crypto Trader Andy Greene
- Microsoft Defender for Cloud Cookbook: Protect multicloud and hybrid cloud environments, manage compliance and strengthen security posture Sasha Kranjac
- Femte kollusionen Denise Rudberg
4.3
- Den sista utposten Mari Jungstedt
4.1
- Han ägde mig: En sann berättelse om att överleva en mans våld Leone Milton
4.1
- De fenomenala fruntimren på Grand Hôtel Ruth Kvarnström-Jones
4.5
- Sångfågeln Anki Edvinsson
4.1
- Omega Lina Areklew
3.8
- Olivträdet Lucinda Riley
4.1
- Det slutar med oss Colleen Hoover
4.2
- Krigarhjärta Lars Wilderäng
3.9
- Sömngångaren Lars Kepler
4.2
- Långfredagen Sofie Sarenbrant
3.8
- Offer i frack Carin Hjulström
4.3
- Kanske i morgon Guillaume Musso
4.4
- Fyrklövern Micke Hansen
4.3
- Är det nu jag dör? Victoria Berggren
3.9
Därför kommer du älska Storytel:
1 miljon stories
Lyssna och läs offline
Exklusiva nyheter varje vecka
Kids Mode (barnsäker miljö)
Flex
För dig som vill prova Storytel.
1 konto
20 timmar/månad
Spara upp till 100 olyssnade timmar
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Premium
För dig som lyssnar och läser ofta.
1 konto
100 timmar/månad
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Unlimited
För dig som vill lyssna och läsa obegränsat.
1 konto
Lyssna obegränsat
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Family
För dig som vill dela stories med hela familjen.
2-6 konton
100 timmar/månad för varje konto
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
2 konton
239 kr /månadSvenska
Sverige