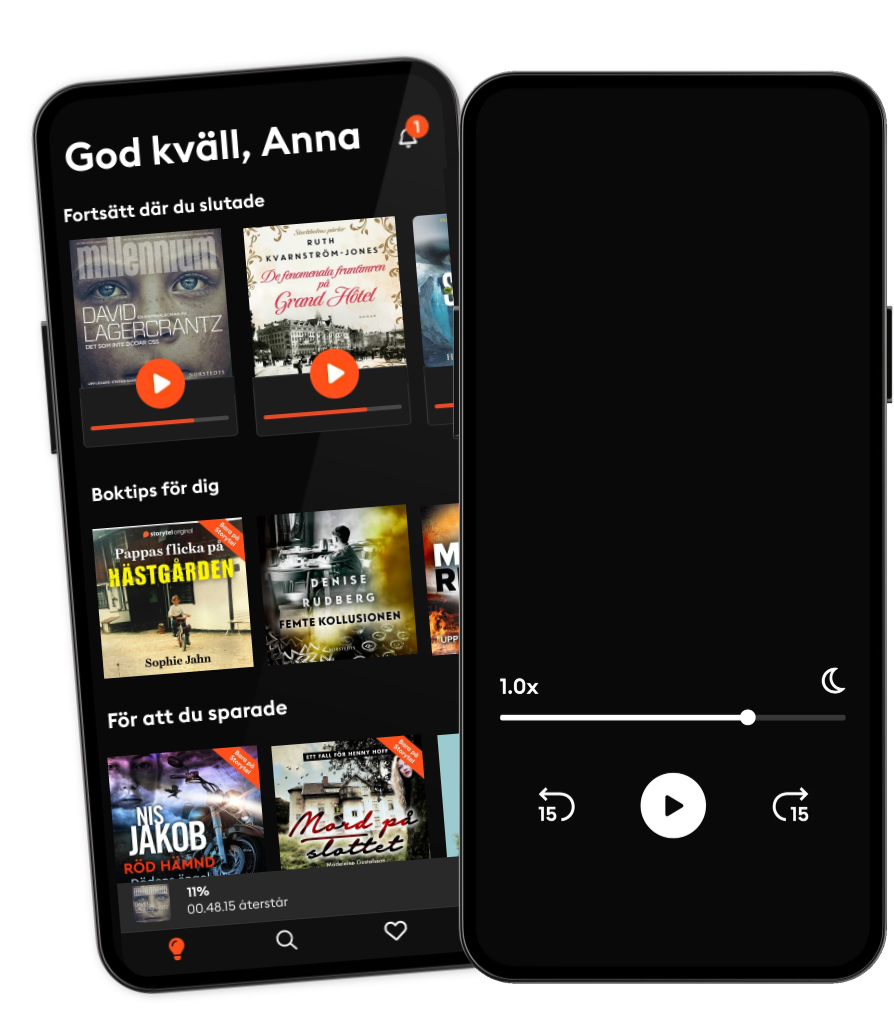
Lyssna när som helst, var som helst
Kliv in i en oändlig värld av stories
- 1 miljon stories
- Hundratals nya stories varje vecka
- Få tillgång till exklusivt innehåll
- Avsluta när du vill
Ethical Hacking Bible: Cybersecurity, Cryptography, Network Security, Wireless Technology and Wireless Hacking with Kali Linux | 7 books in 1
- Av
- Med
- Förlag
- Längd
- 26T 5min
- Språk
- Engelska
- Format
- Kategori
Ekonomi & Business
This Audiobook Bundle Includes 7 Books:
• Book 1 - 25 Most Common Security Threats & How To Avoid Them • Book 2 - 21 Steps For Implementing The Nist Cybersecurity Framework • Book 3 - Cryptography Fundamentals & Network Security • Book 4 - How to Get Into Cybersecurity Without Technical Background • Book 5 - Wireless Technology Fundamentals • Book 6 - Learn Fast How To Hack Any Wireless Networks • Book 7 - Learn Fast How To Hack Like A Pro
Both Wired and Wireless Pen Testing has become a key skill amongst professional hackers using Kali Linux. If you want to become a Cybersecurity Professional, Ethical Hacker, or a Penetration Tester,
BUY THIS AUDIOBOOK NOW AND GET STARTED TODAY!
This Book will cover:
• Cross Site Scripting, Cross-site forgery request, Viruses & Malware • ARP Poisoning, Rogue Access Points, Man in the Middle on Wireless Networks • De-Authentication Attack, Wireless Collision Attack, Wireless Replay Attacks • Access Control Deployments, Data in Transit Security, IDS & IPS Systems & Proxy Servers • Cryptography Basics, Hashing & MD5 Checksum, Hash Algorithms and Encryption Basics • PenTest Tools / Wireless Adapters & Wireless Cards for Penetration Testing • How to implement MITM Attack with Ettercap, How to deploy Rogue Access Point using MITM Attack • How to deploy Evil Twin Deauthentication Attack with mdk3, How to deploy DoS Attack with MKD3 • How to implement Dictionary Attack with Airodump-ng, How to deploy ARP Poisoning with EtterCAP • How to implement MITM Attack with Ettercap & SSLstrip, How to Manipulate Packets with Scapy • How to deploy Deauthentication Attack, How to capture IPv6 Packets with Parasite6 and more...
BUY THIS AUDIOBOOK NOW AND GET STARTED TODAY!
© 2021 HUGO HOFFMAN (Ljudbok): 9781664935075
Utgivningsdatum
Ljudbok: 12 juli 2021
Taggar
Andra gillade också ...
- Hacking: How to Hack Alex Wagner
- Cybersecurity, Cryptography And Network Security For Beginners: Learn Fast How To Get A Job In Cybersecurity HUGO HOFFMAN
- Ethical Hacking & Cybersecurity For Beginners: Pen Test Workflow & Lab Building Basics - 2 Books In 1 ATTILA KOVACS
- CISSP And Cybersecurity For Beginners: Penetration Testing And Ethical Hacking Techniques To Defend Your Infrastructure 3 Books In 1 John Knowles
- Ethical Hacking With Kali Linux: Learn Fast How To Penetrate Wired Or Wireless Networks | 2 Books In 1 HUGO HOFFMAN
- Cybersecurity For Beginners: How To Implement The NIST Framework To Guard Against The Most Common Security Threats | 2 Books In 1 HUGO HOFFMAN
- Cybersecurity Program Development for Business: The Essential Planning Guide Chris Moschovitis
- Cybersecurity Fundamentals: How to Establish Effective Security Management Functions John Knowles
- Coders: Who They Are, What They Think and How They Are Changing Our World Clive Thompson
- Cyber Security: How to Protect Your Digital Life, Avoid Identity Theft, Prevent Extortion, and Secure Your Social Privacy in 2020 and beyond Matt Reyes
- Väninnorna på Nordiska Kompaniet Ruth Kvarnström-Jones
4.1
- Ingen Pascal Engman
4.2
- Sömngångaren Lars Kepler
4.2
- Är det nu jag dör? Leone Milton
3.8
- Död mans kvinna Katarina Wennstam
4.3
- Benådaren Viveca Sten
4.1
- De fenomenala fruntimren på Grand Hôtel Ruth Kvarnström-Jones
4.5
- Kodnamn Verdandi Mikael Ressem
3.6
- Drottningen Jonas Moström
3.8
- De döda och de levande Anders Nilsson
4.3
- Älskade jävla unge Pernilla Pernsjö
4.5
- Livor mortis Mikael Ressem
4
- Grand final Jens Lapidus
4.3
- Anteckningar från aftonsången Jan Guillou
3.5
- IJustWantToBeCool – Del 1, Hans päron IJustWantToBeCool
4.6
Därför kommer du älska Storytel:
1 miljon stories
Lyssna och läs offline
Exklusiva nyheter varje vecka
Kids Mode (barnsäker miljö)
Premium
Lyssnar och läs ofta.
1 konto
100 timmar/månad
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Unlimited
Lyssna och läs obegränsat.
1 konto
Lyssna obegränsat
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Family
Dela stories med hela familjen.
2-6 konton
100 timmar/månad för varje konto
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
2 konton
239 kr /månadFlex
Lyssna och läs ibland – spara dina olyssnade timmar.
1 konto
20 timmar/månad
Spara upp till 100 olyssnade timmar
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Betyg och recensioner
Samlade recensioner
4
Helhetsbetyg baserat på 144 betyg
Andra beskrev boken så här:
Inspiring
Motivating
Informative
Ladda ner appen för att vara med i snacket och lämna recensioner.
Svenska
Sverige