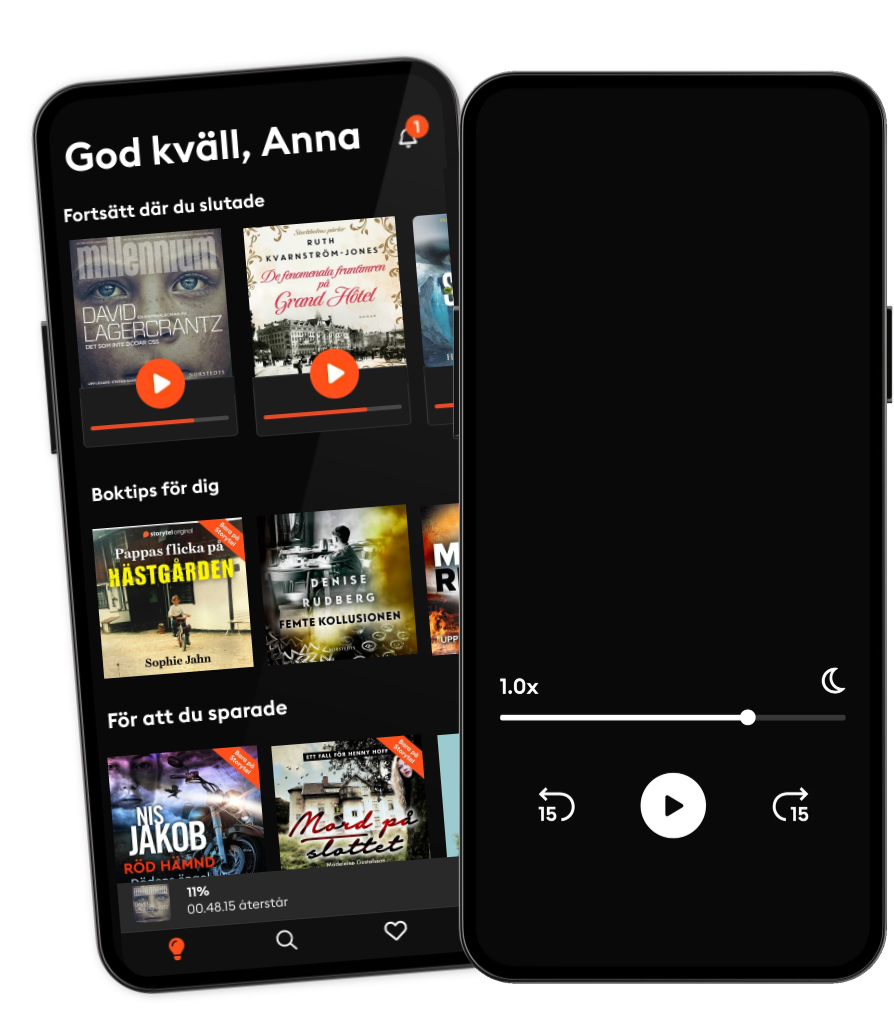
Lyssna när som helst, var som helst
Kliv in i en oändlig värld av stories
- 1 miljon stories
- Hundratals nya stories varje vecka
- Få tillgång till exklusivt innehåll
- Avsluta när du vill
Cyber Security: Beginners’ Guide to Hacking, Phishing, Social Engineering, and Malware
- Längd
- 51min
- Språk
- Engelska
- Format
- Kategori
Fakta
To effectively defend against the threats, cybersecurity professionals employ a variety of strategies and technologies. This includes implementing robust firewalls and intrusion detection systems to monitor and control network traffic, deploying antivirus software to detect and remove malicious software, using encryption to secure sensitive data both in transit and at rest, and implementing strong authentication mechanisms such as multi-factor authentication to prevent unauthorized access.
Additionally, cybersecurity involves ongoing monitoring and analysis of network activity to detect and respond to potential threats in real-time. This may involve the use of security information and event management (SIEM) systems, which aggregate and analyze data from various sources to identify suspicious behavior and security incidents.
Furthermore, cybersecurity professionals often engage in vulnerability assessments and penetration testing to identify weaknesses in systems and networks before they can be exploited by attackers. This proactive approach helps organizations strengthen their defenses and reduce the risk of successful cyber attacks.
© 2024 Freegulls Publishing House LLC (Ljudbok): 9798882425097
Utgivningsdatum
Ljudbok: 8 juni 2024
Andra gillade också ...
- Navigating Cybersecurity: Defending Against Cyber Threats: Strategies for a Secure Online Environment Olivia Larson
- Cyber Security: How to Protect Your Digital Life, Avoid Identity Theft, Prevent Extortion, and Secure Your Social Privacy in 2020 and beyond Matt Reyes
- Cyber Security: Learn All the Essentials and Basic Ways to Avoid Cyber Risk for Your Business. Cyber Security Guide for Beginners (2021 Edition) Cole Peters
- The Promise of Cybersecurity: From Prevention to Response: Building a Fortified Cyber Environment Olivia Martinez
- Ethical Hacking With Kali Linux: Learn Fast How To Penetrate Wired Or Wireless Networks | 2 Books In 1 HUGO HOFFMAN
- See Yourself in Cyber: Security Careers Beyond Hacking Ed Adams
- Computer Skills: Understanding Computer Science and Cyber Security (2 in 1) Jonathan Rigdon
- Cybersecurity, Cryptography And Network Security For Beginners: Learn Fast How To Get A Job In Cybersecurity HUGO HOFFMAN
- CISM Elevate Your Security Skills: Secrets to Transformative Success: "Elevate your CISM skills with dynamic audio lessons that unlock transformative success in your security career!" Orson Penhallow
- Cyber Sentinel: Bulletproofing Your Digital Defenses: Protecting Your Online Presence from Cyber Threats Rachel Evans
- Sömngångaren Lars Kepler
4.2
- De döda och de levande Anders Nilsson
4.3
- Benådaren Viveca Sten
4.1
- Hämnerskan Dag Öhrlund
3.9
- Älskade Betty Katarina Widholm
4.3
- Hundra dagar i juli Emelie Schepp
4
- De fenomenala fruntimren på Grand Hôtel Ruth Kvarnström-Jones
4.5
- Är det nu jag dör? Leone Milton
3.8
- Väninnorna på Nordiska Kompaniet Ruth Kvarnström-Jones
4.1
- Hembiträdet Freida McFadden
4.2
- Död mans kvinna Katarina Wennstam
4.3
- Lokattens klor Karin Smirnoff
3.2
- Ingen Pascal Engman
4.2
- Avhopparen: En sann berättelse Fredrik Thorén
4
- Drottningen Jonas Moström
3.8
Därför kommer du älska Storytel:
1 miljon stories
Lyssna och läs offline
Exklusiva nyheter varje vecka
Kids Mode (barnsäker miljö)
Premium
För dig som lyssnar och läser ofta.
1 konto
100 timmar/månad
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Unlimited
För dig som vill lyssna och läsa obegränsat.
1 konto
Lyssna obegränsat
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Family
För dig som vill dela stories med hela familjen.
2-6 konton
100 timmar/månad för varje konto
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
2 konton
239 kr /månadFlex
För dig som vill prova Storytel.
1 konto
20 timmar/månad
Spara upp till 100 olyssnade timmar
Exklusivt innehåll varje vecka
Avsluta när du vill
Obegränsad lyssning på podcasts
Svenska
Sverige