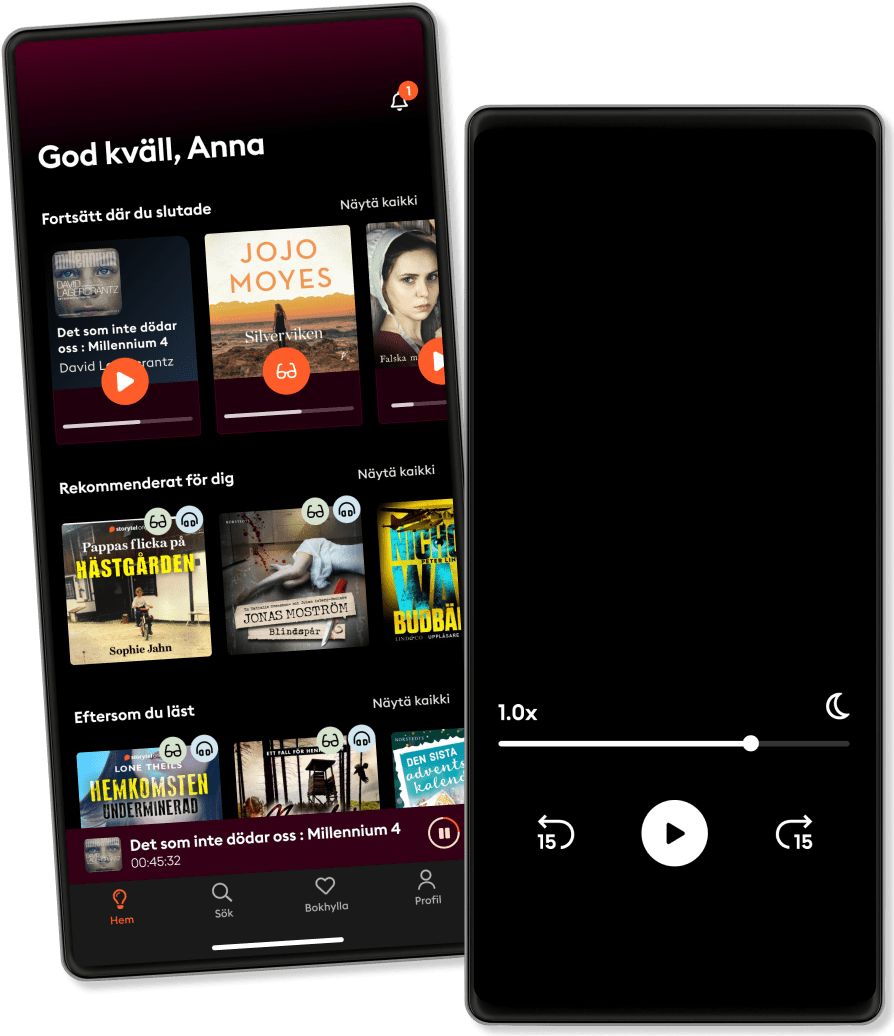
Escucha y lee
Entra en un mundo infinito de historias
- Vive la experiencia de leer y escuchar todo lo que quieras
- Más de 650.000 títulos
- Títulos en exclusiva y Storytel Originals
- Primeros 14 días gratis, luego 8,99 €/mes
- Cancela cuando quieras
Effective Threat Investigation for SOC Analysts: The ultimate guide to examining various threats and attacker techniques using security logs
- Por
- Editorial
- Idioma
- Inglés
- Format
- Categoría
No ficción
Effective threat investigation requires strong technical expertise, analytical skills, and a deep understanding of cyber threats and attacker techniques. It's a crucial skill for SOC analysts, enabling them to analyze different threats and identify security incident origins. This book provides insights into the most common cyber threats and various attacker techniques to help you hone your incident investigation skills. The book begins by explaining phishing and email attack types and how to detect and investigate them, along with Microsoft log types such as Security, System, PowerShell, and their events. Next, you’ll learn how to detect and investigate attackers' techniques and malicious activities within Windows environments. As you make progress, you’ll find out how to analyze the firewalls, flows, and proxy logs, as well as detect and investigate cyber threats using various security solution alerts, including EDR, IPS, and IDS. You’ll also explore popular threat intelligence platforms such as VirusTotal, AbuseIPDB, and X-Force for investigating cyber threats and successfully build your own sandbox environment for effective malware analysis. By the end of this book, you’ll have learned how to analyze popular systems and security appliance logs that exist in any environment and explore various attackers' techniques to detect and investigate them with ease.
© 2023 Packt Publishing (ebook ): 9781837638758
Fecha de lanzamiento
ebook : 25 de agosto de 2023
Etiquetas
Otros también disfrutaron ...
- 8 Steps to Better Security: A Simple Cyber Resilience Guide for Business Kim Crawley
- CISSP Exam Study Guide For Information Security Professionals: Beginners Guide To Cybersecurity Threats, Ethical Hacking And Defense Techniques 3 Books In 1 John Knowles
- Cybersecurity Career Master Plan: Proven techniques and effective tips to help you advance in your cybersecurity career Dr. Gerald Auger
- A Leader’s Guide to Cybersecurity: Why Boards Need to Lead-And How to Do It Jack J. Domet
- Cybersecutity First Principles Rick Howard
- Cyber Crisis: Protecting Your Business from Real Threats in the Virtual World Eric Cole
- Cyber Security: How to Protect Your Digital Life, Avoid Identity Theft, Prevent Extortion, and Secure Your Social Privacy in 2020 and beyond Matt Reyes
- Hacking the Hacker: Learn From the Experts Who Take Down Hackers Roger A. Grimes
- CISSP Exam Study Guide For Cybersecurity Professionals: 2 Books In 1: Beginners Guide To Nist Cybersecurity Framework & Risk Management Governance Strategies HUGO HOFFMAN
- The Art of Deception: Controlling the Human Element of Security William L. Simon
- Las que no duermen NASH Dolores Redondo
4.6
- Victoria: Premio Planeta 2024 Paloma Sánchez-Garnica
4.6
- Las hijas de la criada: Premio Planeta 2023 Sonsoles Ónega
4.4
- Juego de silencios Eva Cornudella
3.5
- Mi recuerdo es más fuerte que tu olvido: Premio de Novela Fernando Lara 2016 Paloma Sánchez-Garnica
4.4
- El lejano país de los estanques Lorenzo Silva
4.1
- La casa en el mar más azul TJ Klune
4.5
- Por si un día volvemos María Dueñas
4.6
- Cómo mandar a la mierda de forma educada - En 10 Minutos. M.Casanova
4.3
- Hôzuki, la librería de Mitsuko Aki Shimazaki
4.2
- La saga de los longevos 2. Los Hijos de Adán Eva García Sáenz de Urturi
4.5
- Resolvemos asesinatos Richard Osman
4.2
- La reina sin espejo Lorenzo Silva
4.3
- El alquimista impaciente Lorenzo Silva
4.1
- La brisa de oriente Paloma Sánchez-Garnica
4.5
Elige el plan:
Más de 650.000 títulos
Kids mode
Modo sin conexión
Cancela cuando quieras
Unlimited
Para los que quieren escuchar y leer sin límites.
1 cuenta
Acceso ilimitado
Escucha y lee los títulos que quieras
Modo sin conexión + Kids Mode
Cancela en cualquier momento
Family
Para los que quieren compartir historias con su familia y amigos.
2-3 cuentas
Acceso ilimitado
Escucha y lee los títulos que quieras
Modo sin conexión + Kids Mode
Cancela en cualquier momento
2 cuentas
15.99 € /mesEspañol
España