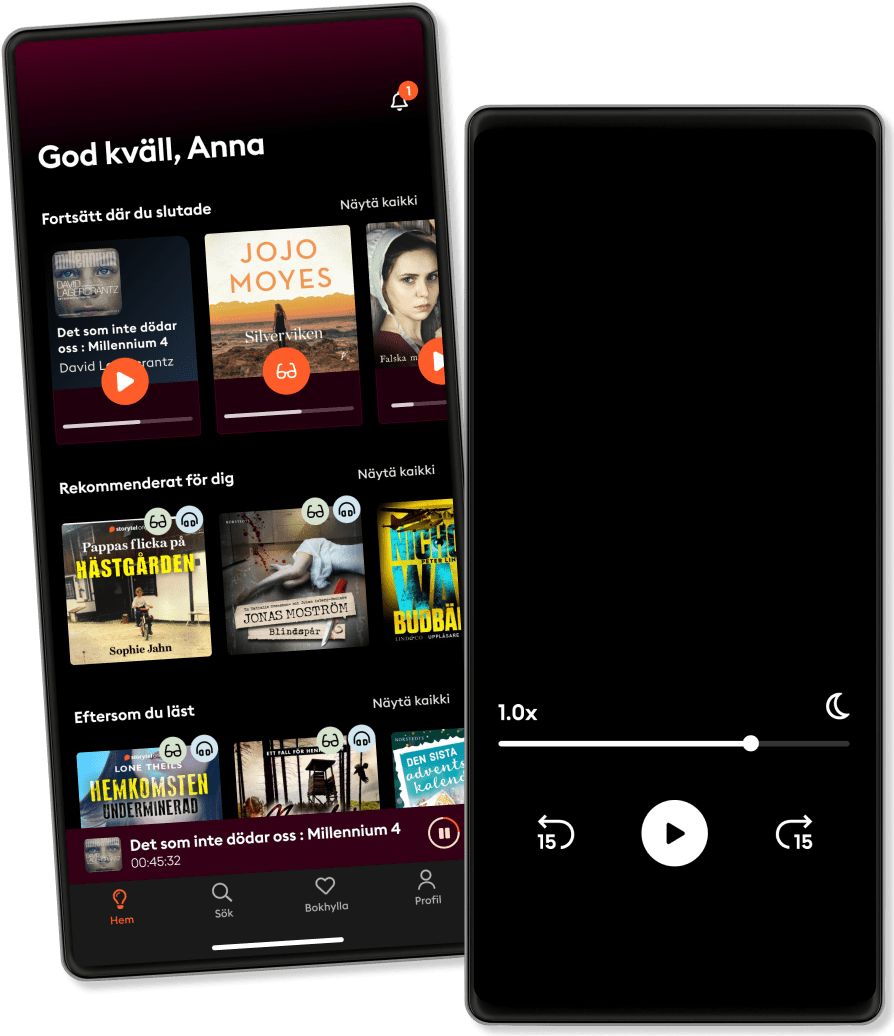
الاستماع والقراءة
خطوة إلى عالم لا حدود له من القصص
- اقرأ واستمع إلى ما تريده
- أكثر من مليون عنوان
- العناوين الحصرية + أصول القصة
- 7 الشهر يورو في EGP89 يوم تجربة مجانية، ثم
- من السهل الإلغاء في أي وقت
Zero Trust Networks: Building Secure Systems in Untrusted Networks (2nd Edition)
- المدة
- 12H 5دقيقة
- اللغة
- اللغة الإنجليزية
- Format
- الفئة
كتب واقعية
Perimeter defenses guarding your network aren't as secure as you might think. Hosts behind the firewall have no defenses of their own, so when a host in the "trusted" zone is breached, access to your data center is not far behind. This practical book introduces you to the zero trust model, a method that treats all hosts as if they're internet-facing, and considers the entire network to be compromised and hostile.
In this updated edition, the authors show you how zero trust lets you focus on building strong authentication, authorization, and encryption throughout, while providing compartmentalized access and better operational agility. You'll learn the architecture of a zero trust network, including how to build one using currently available technology.
You'll also explore fundamental concepts of a zero trust network, including trust engine, policy engine, and context aware agents; discover how this model embeds security within the system's operation, rather than layering it on top; use existing technology to establish trust among the actors in a network; migrate from a perimeter-based network to a zero trust network in production; examine case studies that provide insights into various organizations' zero trust journeys; and learn about the various zero trust architectures, standards, and frameworks.
© 2024 Ascent Audio (دفتر الصوت ): 9781663735584
تاريخ الإصدار
دفتر الصوت : ٤ يونيو ٢٠٢٤
الوسوم
واستمتع آخرون أيضًا...
- (ISC)2 CCSP Certified Cloud Security Professional Official Study Guide: 2nd Edition Ben Malisow
- 8 Steps to Better Security: A Simple Cyber Resilience Guide for Business Kim Crawley
- Cybersecurity Fundamentals: How to Establish Effective Security Management Functions John Knowles
- Cybersecutity First Principles Rick Howard
- Certified Information Security Manager CISM Study Guide Mike Chapple, PhD, CISM
- Project Zero Trust: A Story about a Strategy for Aligning Security and the Business George Finney
- Building a Cyber Risk Management Program: Evolving Security for the Digital Age Brian Allen
- Cloud Security For Dummies Ted Coombs
- The Reign of Botnets: Defending Against Abuses, Bots and Fraud on the Internet David Senecal
- CISSP Exam Study Guide For Information Security Professionals: Beginners Guide To Cybersecurity Threats, Ethical Hacking And Defense Techniques 3 Books In 1 John Knowles
- أسطورة أحمد خالد توفيق - E01 خلف جابر
4.4
- ملخص كتاب كيف تتحدث مع أي شخص 92 خدعة صغيرة: اثنتان وتسعون خدعة صغيرة، لنجاح كبير في العلاقات ليل لاوندز
3.5
- فقط اصمت وافعلها!: كيف تبدأ وتستمر براين تريسي
4.1
- أوراق شمعون المصري الموسم الأول أسامة عبد الرءوف الشاذلي
4.6
- ملخص كتاب عقل هادئ: كيف توقف التوتر وتحدّ من نوبات القلق وتقضي على التفكير السلبي ستيف سكوت
4.3
- المطارد حسن الجندي
4.5
- أرض زيكولا عمرو عبدالحميد
4.1
- فاتتني صلاة (الإصدار الصوتي الثاني) إسلام جمال
4.8
- القيصر: التاريخ السري لفلاديمير بوتين طاهر المعتز بالله
4.5
- بضع ساعات في يوم ما محمد صادق
2.8
- النباتية هان كانغ
3
- ملخص كتاب الذكاء العاطفي ترافيس برادبيري
3.5
- العادات الذرية جيمس كلير
4.5
- فن اللامبالاة: لعيش حياة تخالف المألوف مارك مانسون
4.3
- 30 يوما مع الله فيصل أحمد بخاري
4.6
ما مميزات اشتراك Storytel؟
أكثر من 200000 عنوان
وضع الأطفال (بيئة آمنة للأطفال)
تنزيل الكتب للوصول إليها دون الاتصال بالإنترنت
الإلغاء في أي وقت
شهري
قصص لكل المناسبات.
حساب واحد
حساب بلا حدود
1 حساب
استماع بلا حدود
إلغاء في أي وقت
سنويا
قصص لكل المناسبات.
حساب واحد
حساب بلا حدود
1 حساب
استماع بلا حدود
إلغاء في أي وقت
6 أشهر
قصص لكل المناسبات.
حساب واحد
حساب بلا حدود
1 حساب
استماع بلا حدود
إلغاء في أي وقت
عربي
مصر