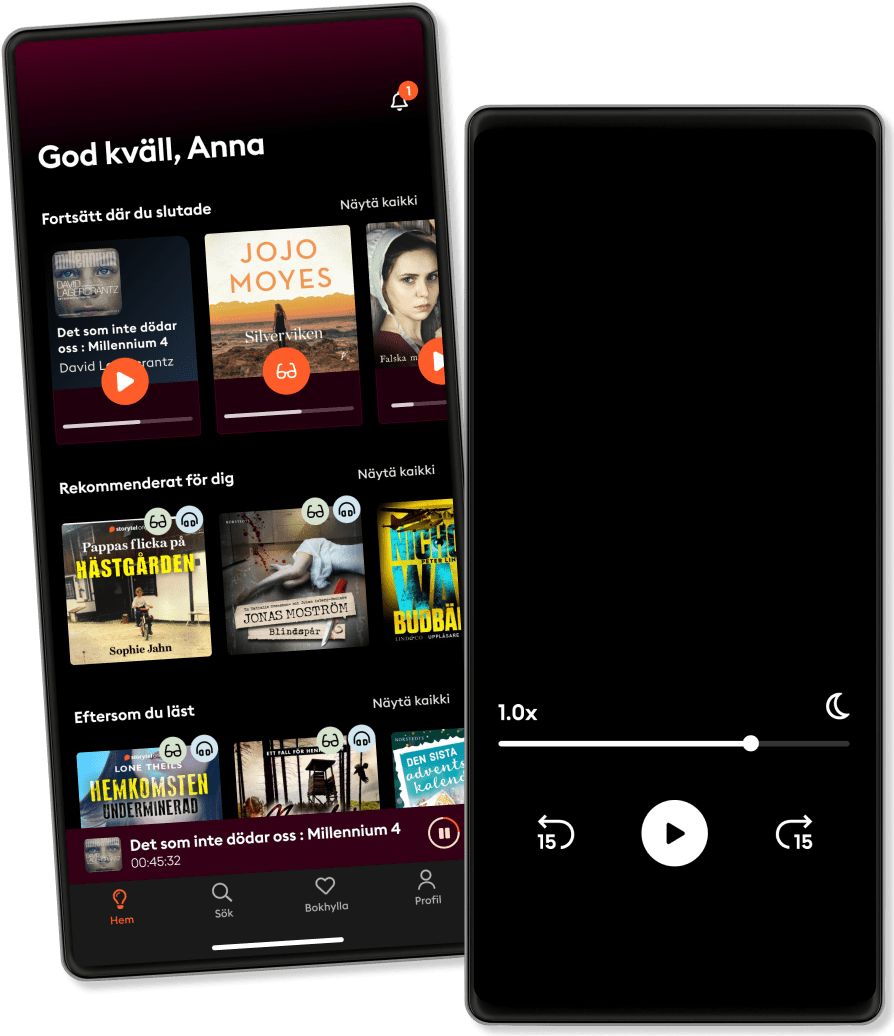
الاستماع والقراءة
خطوة إلى عالم لا حدود له من القصص
- اقرأ واستمع إلى ما تريده
- أكثر من مليون عنوان
- العناوين الحصرية + أصول القصة
- 7 الشهر يورو في EGP89 يوم تجربة مجانية، ثم
- من السهل الإلغاء في أي وقت
Security Architecture A Complete Guide - 2024 Edition
- بواسطة
- الناشر
- اللغة
- اللغة الإنجليزية
- Format
- الفئة
الإدارة والأعمال
Are various forms of media covered and protected under existing policies and procedures?
Do you ensure that mobile users access only appropriate resources throughout the network?
Is the system compatible with your organizations current security architecture?
Should your security architecture be solely reliant on patching vulnerabilities?
What are the top areas of IT and security overspending that you are seeing in the market?
What is the difference between an ISMS and an enterprise security architecture?
What must you do before your sensor can initiate blocking via your infrastructure devices?
What representation format is used to exchange security information between applications?
What type of information does or would your organization share with other companies/firms?
Will users be informed in writing if the cloud is to make changes to the security architecture?
This Security Architecture Guide breaks away from traditional books. If you're seeking a standard textbook, this may not be the right fit for you. This guide along with its accompanying digital resources is for you who understands the importance of asking profound questions. This equips you with the questions necessary to uncover the Security Architecture challenges you're confronting and devise superior solutions to address these issues.
Defining, designing, creating, and implementing a process to solve a challenge or achieve an objective is the most valuable role… Get Stuff Done in EVERY group, company, organization and department.
Unless you are dealing with a one-time, single-use project, there should be a process. That process needs to be designed by someone with a broad enough perspective to ask the right questions. Someone able to ask the right questions and step back and say, 'What are we really trying to accomplish here? And is there a different way to look at it?'
This Self-Assessment empowers people to do just that - whether their title is entrepreneur, manager, consultant, (Vice-)President, CxO etc... - they are the people who shape the future. They are the person who asks the right questions to make Security Architecture investments work better.
This Security Architecture All-Inclusive Self-Assessment enables You to be that person.
INCLUDES all the tools you need to an in-depth Security Architecture Self-Assessment. Featuring new and updated case-based questions, organized into seven core levels of Security Architecture maturity, this Self-Assessment will help you identify areas in which Security Architecture improvements can be made.
In using the questions you will be better able to:
Assess Security Architecture projects, initiatives, organizations, businesses and processes using established diagnostic standards and practices.
Implement evidence-based best practice strategies aligned with overall goals.
Integrate recent advances in Security Architecture and process design strategies into practice according to best practice guidelines.
Using the Self-Assessment tool gives you the Security Architecture Scorecard, enabling you to develop a clear picture of which Security Architecture areas need attention.
Your purchase includes access to the Security Architecture self-assessment digital components which gives you your dynamically prioritized project-ready tool. This tool enables you to define, show and lead your organization exactly with what's important.
© 2023 5STARCooks (كتاب ): 9781038812513
تاريخ الإصدار
كتاب : ٧ نوفمبر ٢٠٢٣
واستمتع آخرون أيضًا...
- Platform Architecture A Complete Guide - 2021 Edition Gerardus Blokdyk
- Enterprise Information Security Architecture A Complete Guide - 2021 Edition Gerardus Blokdyk
- Enterprise API Management: Design and deliver valuable business APIs Luis Weir
- Solutions Architect's Handbook: Kick-start your career as a solutions architect by learning architecture design principles and strategies Saurabh Shrivastava
- Security Architecture A Complete Guide - 2021 Edition Gerardus Blokdyk
- The End of the World is Just the Beginning: Mapping the Collapse of Globalization Peter Zeihan
- Pentaho 8 Reporting for Java Developers Francesco Corti
- AWS DevOps Simplified: Build a solid foundation in AWS to deliver enterprise-grade software solutions at scale Akshay Kapoor
- CISM Certification: Certified Information Security Manager Exam Prep 2024-2025: Ace Your CISM Exam on the First Attempt | 200+ Engaging Q&A | Realistic Practice Questions and Detailed Answer Explanations Thaddeus Greyson
- The Quitter's Manifesto: Quit a Job You Hate for the Work You Love Pat Hiban
- أسطورة أحمد خالد توفيق - E01 خلف جابر
4.4
- ملخص كتاب الذكاء العاطفي ترافيس برادبيري
3.3
- ملخص كتاب عقل هادئ: كيف توقف التوتر وتحدّ من نوبات القلق وتقضي على التفكير السلبي ستيف سكوت
4.3
- أرض زيكولا عمرو عبدالحميد
4.1
- ملخص كتاب قوانين الكاريزما كيرت مورتنسن
3.8
- ملخص كتاب فن اللامبالاة مارك مانسون
3.7
- ملخص كتاب كيف تتحدث مع أي شخص 92 خدعة صغيرة: اثنتان وتسعون خدعة صغيرة، لنجاح كبير في العلاقات ليل لاوندز
3.6
- أوراق شمعون المصري الموسم الأول أسامة عبد الرءوف الشاذلي
4.7
- ملخص كتاب دماغك تحت تأثير الإباحية غاري ويلسون
4.2
- معاطي Nani Abu Rawash
4.1
- المطارد حسن الجندي
4.5
- أغنية الجليد والنار: لعبة العروش جورج ر. ر. مارتن
4.6
- 30 يوما مع الله فيصل أحمد بخاري
4.6
- العادات الذرية جيمس كلير
4.5
- فن اللامبالاة: لعيش حياة تخالف المألوف مارك مانسون
4.3
ما مميزات اشتراك Storytel؟
أكثر من 200000 عنوان
وضع الأطفال (بيئة آمنة للأطفال)
تنزيل الكتب للوصول إليها دون الاتصال بالإنترنت
الإلغاء في أي وقت
شهري
قصص لكل المناسبات.
حساب واحد
حساب بلا حدود
1 حساب
استماع بلا حدود
إلغاء في أي وقت
سنويا
قصص لكل المناسبات.
حساب واحد
حساب بلا حدود
1 حساب
استماع بلا حدود
إلغاء في أي وقت
6 أشهر
قصص لكل المناسبات.
حساب واحد
حساب بلا حدود
1 حساب
استماع بلا حدود
إلغاء في أي وقت
عربي
مصر