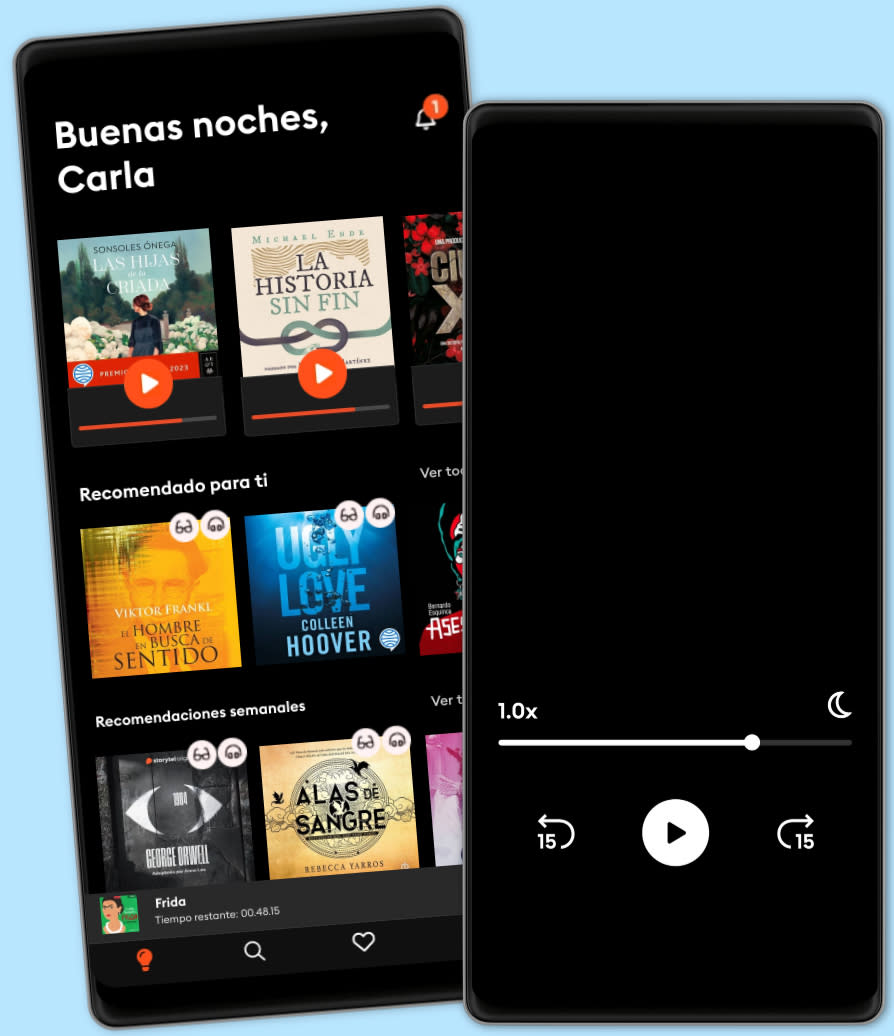
Escucha y lee
Descubre un mundo infinito de historias
- Lee y escucha todo lo que quieras
- Más de 500 000 títulos
- Títulos exclusivos + Storytel Originals
- 14 días de prueba gratis, luego $24,900 COP/al mes
- Cancela cuando quieras
Zero Trust Networks: Building Secure Systems in Untrusted Networks (2nd Edition)
- Duración
- 12H 5min
- Idioma
- Inglés
- Format
- Categoría
No ficción
Perimeter defenses guarding your network aren't as secure as you might think. Hosts behind the firewall have no defenses of their own, so when a host in the "trusted" zone is breached, access to your data center is not far behind. This practical book introduces you to the zero trust model, a method that treats all hosts as if they're internet-facing, and considers the entire network to be compromised and hostile.
In this updated edition, the authors show you how zero trust lets you focus on building strong authentication, authorization, and encryption throughout, while providing compartmentalized access and better operational agility. You'll learn the architecture of a zero trust network, including how to build one using currently available technology.
You'll also explore fundamental concepts of a zero trust network, including trust engine, policy engine, and context aware agents; discover how this model embeds security within the system's operation, rather than layering it on top; use existing technology to establish trust among the actors in a network; migrate from a perimeter-based network to a zero trust network in production; examine case studies that provide insights into various organizations' zero trust journeys; and learn about the various zero trust architectures, standards, and frameworks.
© 2024 Ascent Audio (Audiolibro ): 9781663735584
Fecha de lanzamiento
Audiolibro : 4 de junio de 2024
Etiquetas
Otros también disfrutaron ...
- (ISC)2 CCSP Certified Cloud Security Professional Official Study Guide: 2nd Edition Ben Malisow
- Cybersecurity Fundamentals: How to Establish Effective Security Management Functions John Knowles
- 8 Steps to Better Security: A Simple Cyber Resilience Guide for Business Kim Crawley
- Cybersecutity First Principles Rick Howard
- Certified Information Security Manager CISM Study Guide Mike Chapple, PhD, CISM
- Project Zero Trust: A Story about a Strategy for Aligning Security and the Business George Finney
- Building a Cyber Risk Management Program: Evolving Security for the Digital Age Brian Allen
- Cloud Security For Dummies Ted Coombs
- The Reign of Botnets: Defending Against Abuses, Bots and Fraud on the Internet David Senecal
- CISSP Exam Study Guide For Information Security Professionals: Beginners Guide To Cybersecurity Threats, Ethical Hacking And Defense Techniques 3 Books In 1 John Knowles
- Cómo mandar a la mierda de forma educada - En 10 Minutos. M.Casanova
4.3
- Cómo Hablar Con Cualquier Persona En Cualquier Lugar Y En Cualquier Momento Nina Maxwell
4.3
- Victoria: Premio Planeta 2024 Paloma Sánchez-Garnica
4.6
- Cien años de soledad Gabriel García Márquez
4.6
- Cómo hacer que te pasen cosas buenas: Entiende tu cerebro, gestiona tus emociones, mejora tu vida Marian Rojas Estapé
4.5
- Los secretos de la mente millonaria T. Harv Eker
4.3
- Alas de Hierro Rebecca Yarros
4.3
- Harry Potter y la piedra filosofal J.K. Rowling
4.8
- El Poder de Estar Solo: Una Dosis de Motivación Acompañada de Ideas Revolucionarias Para una Vida Mejor BRIAN ALBA
4.2
- Como hacer que te pasen cosas buenas - En 10 Minutos M.Casanova
4.1
- Alas de sangre Rebecca Yarros
4.5
- Alas de Ónix (Onyx Storm) Rebecca Yarros
4.2
- La ley de la atracción William Walker Atkinson
4.5
- Volver a empezar (It Starts with Us) Colleen Hoover
4.2
- Romper el círculo (It Ends with Us) Colleen Hoover
4.3
Español
Colombia